Reversing: Find The Easy Pass
Introduction
EasyPass is an easy reversing challenge from hack the box.
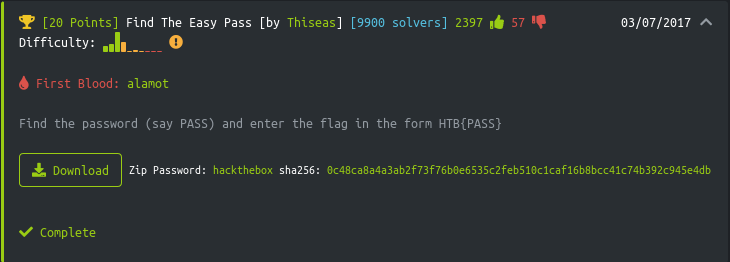
It took about 5 minutes to solve, including time to take screenshots, so indeed it was an EasyPass.
Static Analysis
Downloading and extracting the archive immediatly tells you this will be a Windows challenge. The extension of the file is exe and file confirms that it is a PE32 Executable.
I ran die on the binary to get a better sense of it.
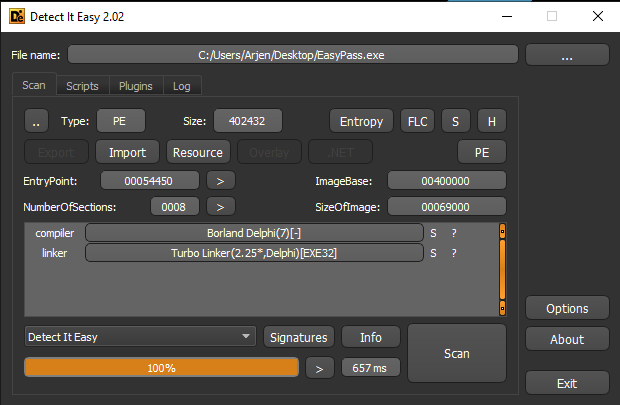
The fact that it is written in Borland Delphi makes me very happy. In my toolbox I have a great tool to work with those type of binaries; Interactive Delphi Reconstructor. It also reminds me of all the years I actually wrote Delphi software, back in the day.
Dynamic Analysis
To get a sense for the application I decided to run it and get a feel for the types of input that are in the challenge.
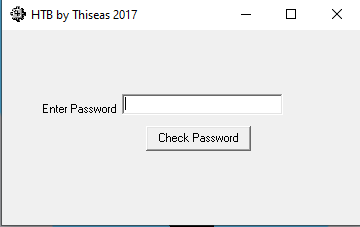
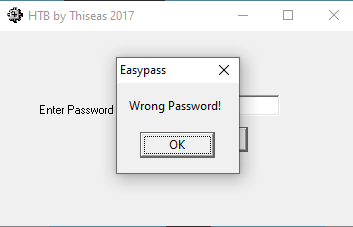
So there is a single input field and an button with the text Check Password. When entering a password a popup will be shown with the text Wrong Password!.
As there is only 1 button on the form it seems that all we need to do is to look for the OnClick function in the code to find out how the passwords are checked.
Static Analysis with IDR
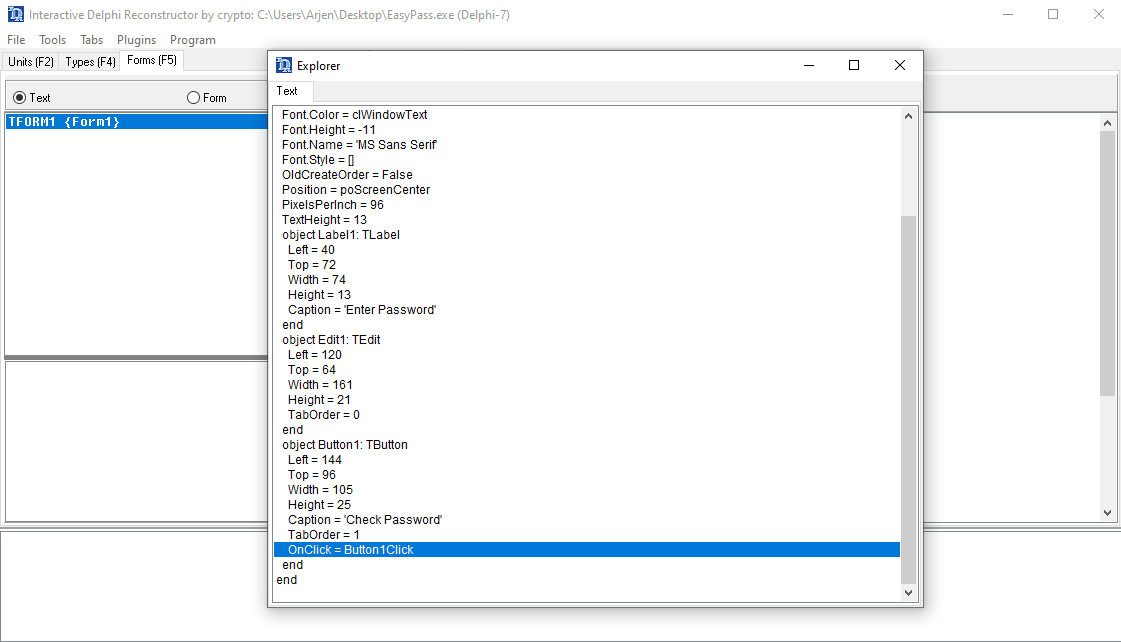
Lets start up IDR and open the binary. In the Forms overview there is only a single form to be found and double clicking it the definition is shown. In the defintion of the form the function Button1Click is connected to our button.
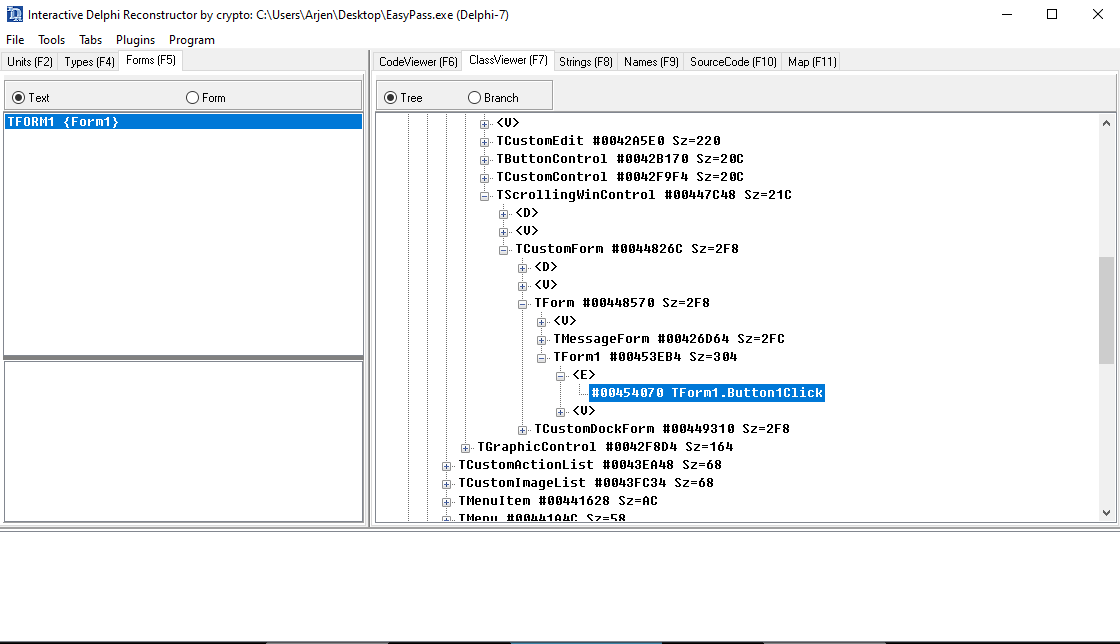
Press F7 to go to the ClassViewer, which basically is the hierarchy of code in the Delphi application. Press Ctrl-F (search) and enter the name of the function, Button1Click.
Double click on the reference in the tree to get to the actual code. It is listed below. Take a look and see if you can guess the password…
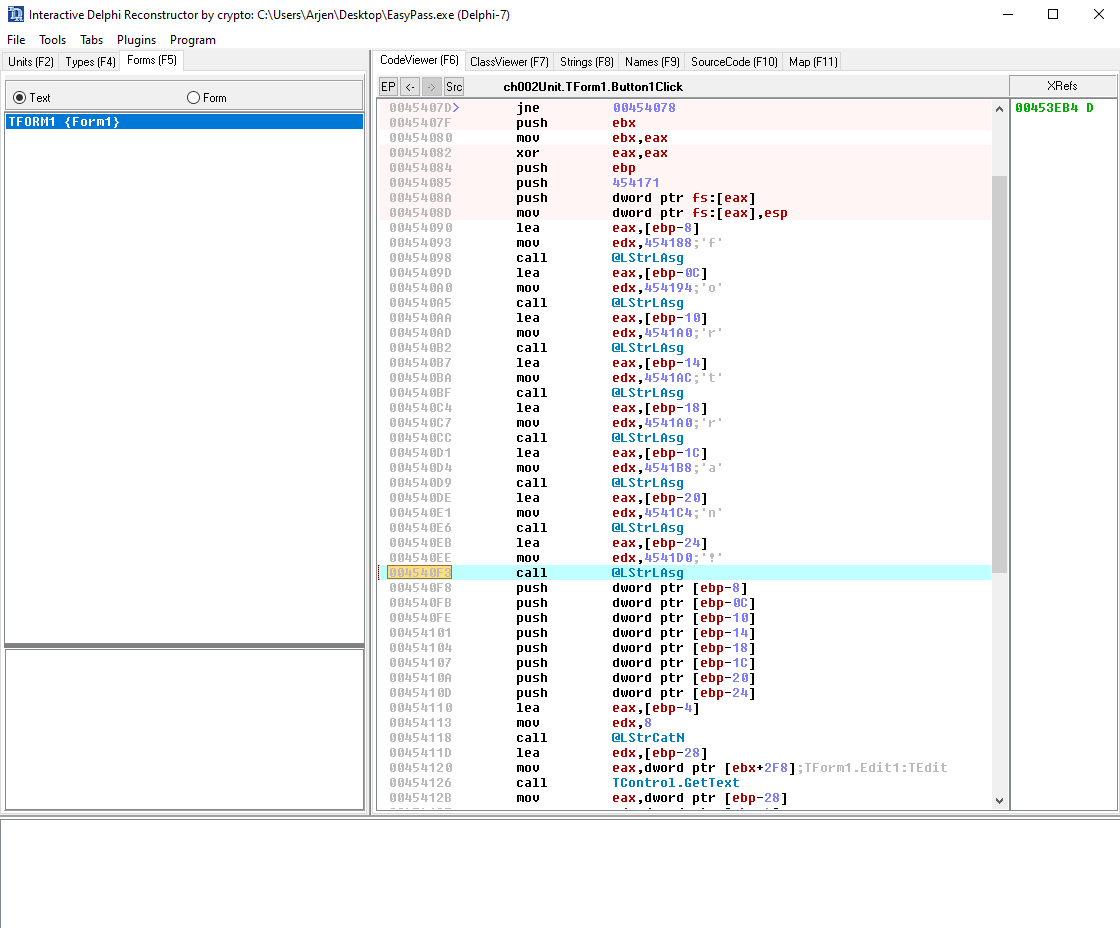
Yes, the list of @LStrLAsg, which basically means a string assignment, is followed by a @LStrCatN, which is the concatenation of the various strings, to form the actual password.
In this case it is as simple as just joining the various assignments into the password fortran!.
And thats that.
