Flare-On 2015 Challenge 3
For challenge 3 the archive extracts to a file called elfie. Immediately I thought it would be a Linux challenge, as Linux file types are ELF files. But die shows something else.
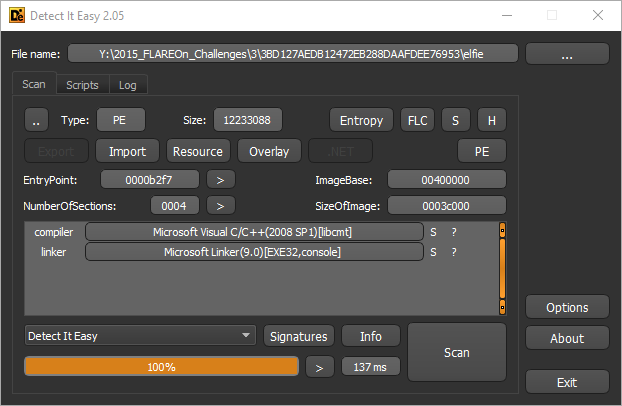
According to die it is an PE, a regular Windows file. So I renamed it to elfie.exe and an application icon shows up. Examining the executable in Resource Hacker shows a more high-res version of the icon.
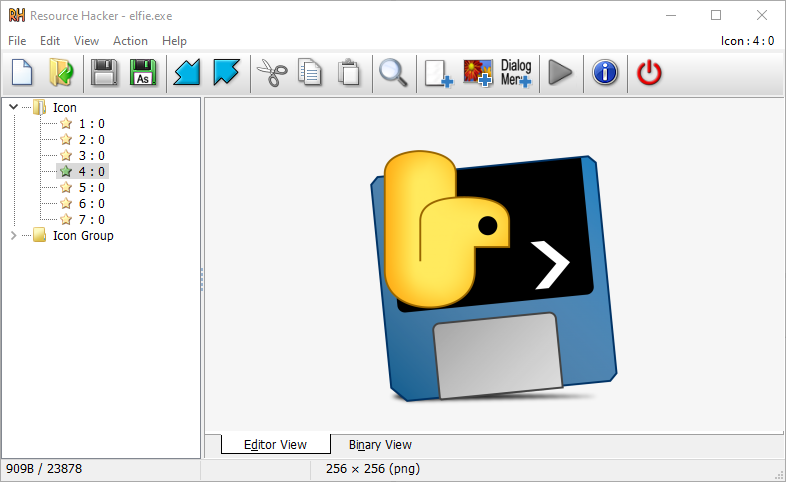
The icon itself is already an hint. The snake on it looks a lot like a Python. You can probably do a reverse image search using the logo and you will end up at the pyinstaller website.
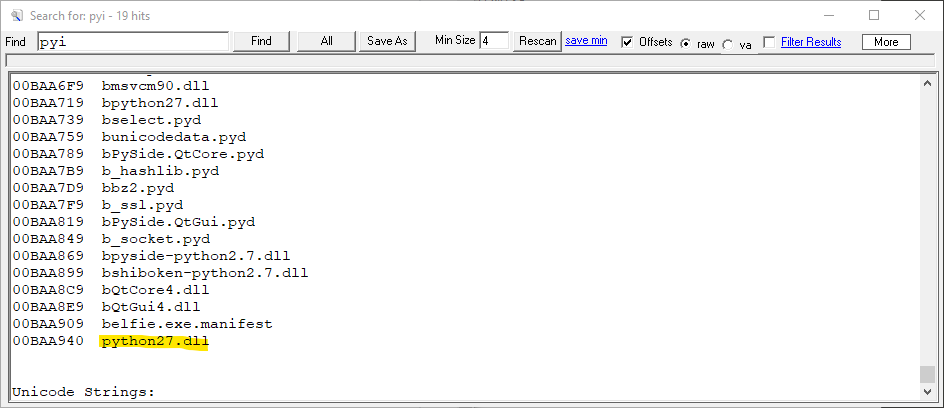
Using strings the python connection can be confirmed.
So, this is actually a Python application in disguise. Generally this is done to make Python application available on platforms where it is unusual to have Python installed, in this case Windows.
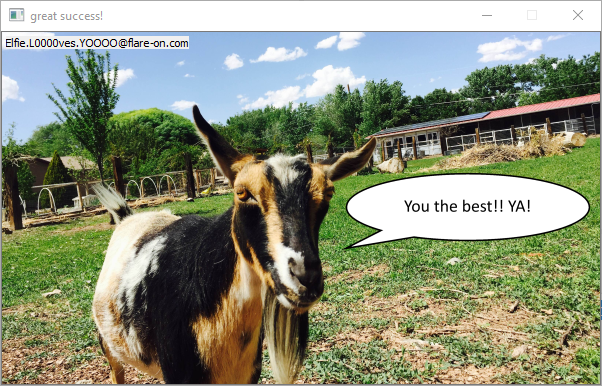
Running the executable, to see what it wants as an input, reveals a goat.

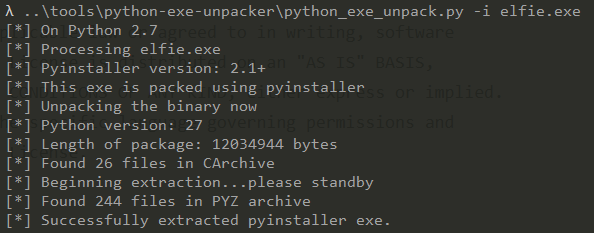
The title of the window is “Look inside you can find one there”, obviously there is a need to get to the original python code for this application. There is a really good project that will unpack py2exe and pyinstaller projects. It is called python-exe-unpacker and is available on Github. After installing it can be used to extract the executable.
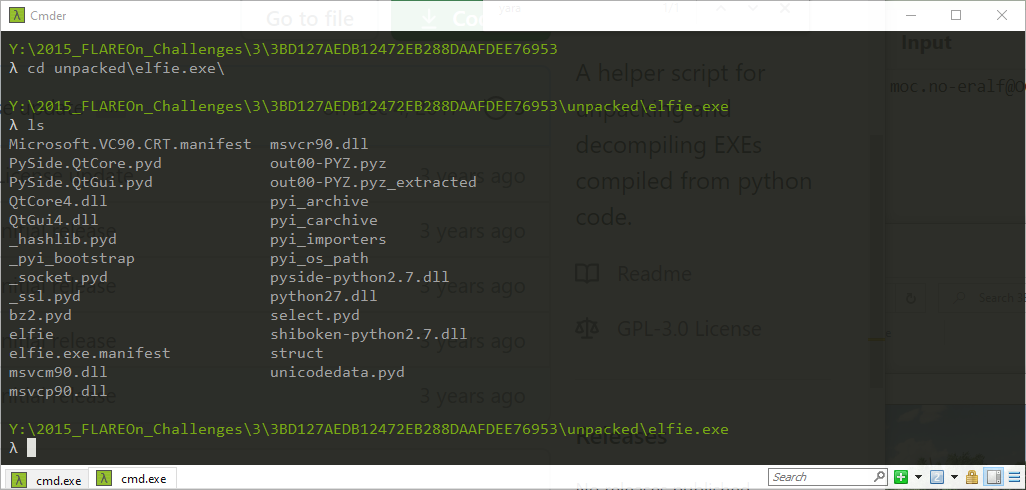
The unpacked structure has some interesting files, elfie and elfie.exe.manifest. Every packed application requires an entry point, in the case of this executable it is elfie.
Examining the elfie file shows that it is ASCII and at first glance it looks like a mistake; there are many lines of encoding and variable assignment. The encoding is Base64.
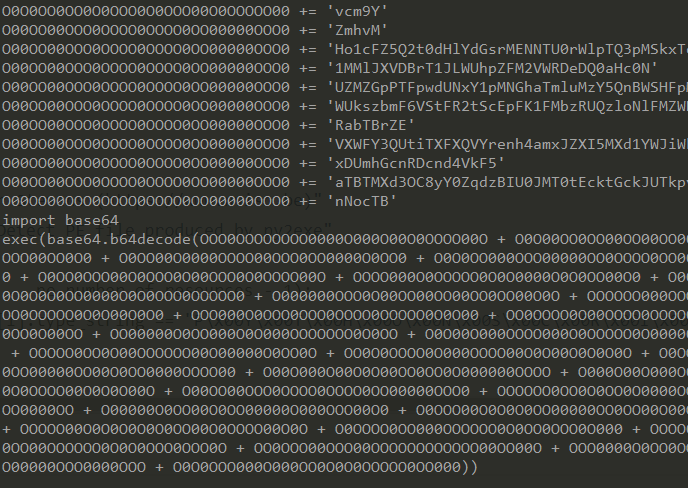
At the end of the file a familiar python statement shows up, import base64 followed by an exec instruction. In order to get the actual source code the exec can be replaced by a print statement. Instead of running the application, it will print the obfuscated source code.
The source code is all on 1 single line, but can be viewed nicely in a decent editor. Scrolling through it a string that looks like a key catches the eye.
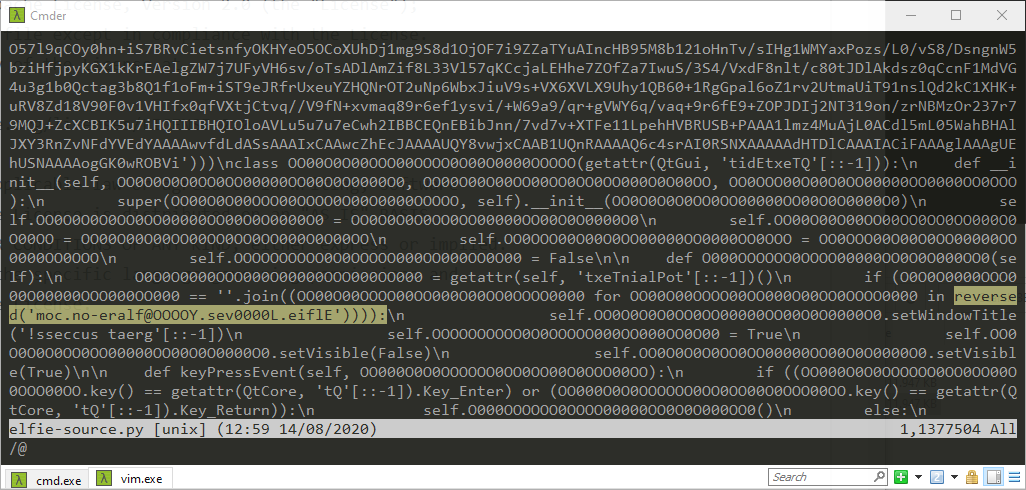
The key is reversed, so undoing that operation reveals the real key. It can be pasted onto the goat and after hitting Enter the goat will offer their congratulations.